Istatistica 1 2 2 – Advanced System Monitor
- Istatistica 1 2 2 – Advanced System Monitor User
- Istatistica 1 2 2 – Advanced System Monitor Calibration
- Istatistica 1 2 2 – Advanced System Monitor Software
IStatistica 1.1.1 (Mac OS X) 2 MBiStatistica is an advanced system monitor for OS X. It includes notification center widget and status bar menu. Simply slide out notification center to kee. IStatistica is an advanced system monitor. It includes a Notification-Center widget and status-bar menu. Simply slide out Notification Center to keep an eye on your CPU, memory, disk usage, and network activity. AMD System Monitor Compatibility: This utility was designed to work with AMD’s new APUs, but will also work with AMD Phenom™ and AMD Athlon™ class processors, as well as AMD class graphics (both discrete and IGP) in combination with a Microsoft Windows® 7 32-bit / 64-bit Edition based system. Oct 08, 2017 iStatistica is an advanced system monitor. It includes a Notification-Center widget and status-bar menu. Simply slide out Notification Center to keep an eye on your CPU, memory, disk usage, and network activity. IStatistica is an advanced system monitor for macOS. It includes notification center widget and status bar menu. Simply slide out notification center to keep an eye on your CPU, memory, disk usage and network activity.
-->Applies to
- Windows 10
This reference for IT professionals provides information about the advanced audit policy settings that are available in Windows and the audit events that they generate.
The security audit policy settings under Security SettingsAdvanced Audit Policy Configuration can help your organization audit compliance with important business-related and security-related rules by tracking precisely defined activities, such as:
- A group administrator has modified settings or data on servers that contain finance information.
- An employee within a defined group has accessed an important file.
- The correct system access control list (SACL) is applied to every file and folder or registry key on a computer or file share as a verifiable safeguard against undetected access.
You can access these audit policy settings through the Local Security Policy snap-in (secpol.msc) on the local computer or by using Group Policy.
These advanced audit policy settings allow you to select only the behaviors that you want to monitor. You can exclude audit results for behaviors that are of little or no concern to you, or behaviors that create an excessive number of log entries. In addition, because security audit policies can be applied by using domain Group Policy Objects, audit policy settings can be modified, tested, and deployed to selected users and groups with relative simplicity.Audit policy settings under Security SettingsAdvanced Audit Policy Configuration are available in the following categories:
Account Logon
Configuring policy settings in this category can help you document attempts to authenticate account data on a domain controller or on a local Security Accounts Manager (SAM). Unlike Logon and Logoff policy settings and events, which track attempts to access a particular computer, settings and events in this category focus on the account database that is used. This category includes the following subcategories:
Istatistica 1 2 2 – Advanced System Monitor User
Account Management
The security audit policy settings in this category can be used to monitor changes to user and computer accounts and groups. This category includes the following subcategories:
Detailed Tracking
Detailed Tracking security policy settings and audit events can be used to monitor the activities of individual applications and users on that computer, and to understand how a computer is being used. This category includes the following subcategories:
DS Access
DS Access security audit policy settings provide a detailed audit trail of attempts to access and modify objects in Active Directory Domain Services (AD DS). These audit events are logged only on domain controllers. This category includes the following subcategories:
Logon/Logoff
Istatistica 1 2 2 – Advanced System Monitor Calibration
Logon/Logoff security policy settings and audit events allow you to track attempts to log on to a computer interactively or over a network. These events are particularly useful for tracking user activity and identifying potential attacks on network resources. This category includes the following subcategories:
Object Access
Object Access policy settings and audit events allow you to track attempts to access specific objects or types of objects on a network or computer. To audit attempts to access a file, directory, registry key, or any other object, you must enable the appropriate Object Access auditing subcategory for success and/or failure events. For example, the file system subcategory needs to be enabled to audit file operations, and the Registry subcategory needs to be enabled to audit registry accesses.
Proving that these audit policies are in effect to an external auditor is more difficult. There is no easy way to verify that the proper SACLs are set on all inherited objects. To address this issue, see Global Object Access Auditing.
This category includes the following subcategories:
Policy Change
Policy Change audit events allow you to track changes to important security policies on a local system or network. Because policies are typically established by administrators to help secure network resources, monitoring changes or attempts to change these policies can be an important aspect of security management for a network. This category includes the following subcategories:
Privilege Use
Permissions on a network are granted for users or computers to complete defined tasks. Privilege Use security policy settings and audit events allow you to track the use of certain permissions on one or more systems. This category includes the following subcategories:
System
System security policy settings and audit events allow you to track system-level changes to a computer that are not included in other categories and that have potential security implications. This category includes the following subcategories:
Global Object Access Auditing
Global Object Access Auditing policy settings allow administrators to define computer system access control lists (SACLs) per object type for the file system or for the registry. The specified SACL is then automatically applied to every object of that type.Auditors will be able to prove that every resource in the system is protected by an audit policy by viewing the contents of the Global Object Access Auditing policy settings. For example, if auditors see a policy setting called 'Track all changes made by group administrators,' they know that this policy is in effect.
Resource SACLs are also useful for diagnostic scenarios. For example, setting the Global Object Access Auditing policy to log all the activity for a specific user and enabling the policy to track 'Access denied' events for the file system or registry can help administrators quickly identify which object in a system is denying a user access.
Note
If a file or folder SACL and a Global Object Access Auditing policy setting (or a single registry setting SACL and a Global Object Access Auditing policy setting) are configured on a computer, the effective SACL is derived from combining the file or folder SACL and the Global Object Access Auditing policy. This means that an audit event is generated if an activity matches the file or folder SACL or the Global Object Access Auditing policy.
This category includes the following subcategories:
iStatistica Pro 3.0.1

iStatistica Pro lets you overview your battery statistics, realtime informations about CPU, RAM usage and much more. Network statistics includes external, gateway and local IPs, speed and data rates chart.
iStatistica Pro offers web-access to track CPU, Memory, Disk and Sensors statistics over local area network. Just enable web-access in application settings and point your browser to Mac's address.
Pro version includes exclusive modules for folders and drives visualization, detailed apps monitoring and more focused on enterprise-level security for remote access.
Features
- System monitoring
- Uptime
- Memory pressure
- CPU usage
- Disk usage
- Ejecting external drives
- Battery information (cycles, health, capacity)
- Network activity
- Storage visualization
- Easily find and remove unneeded files
- Network interfaces dashboard
- Detailed apps statistics
- History of cpu and memory usage
- Temperature and Fans*
- CPU, GPU, memory temperature statistics
- Restrict access by ip and passkey
- Fan speeds
What's New:
Version 3.0- Notifications
- Redesigned Dashboards
- Redesigned disk visualization
- Improved Web-Access
- Improved Bluetooth devices support
- New icon
- macOS Big Sur support
- Universal Binary
- Bugfixes and improvements
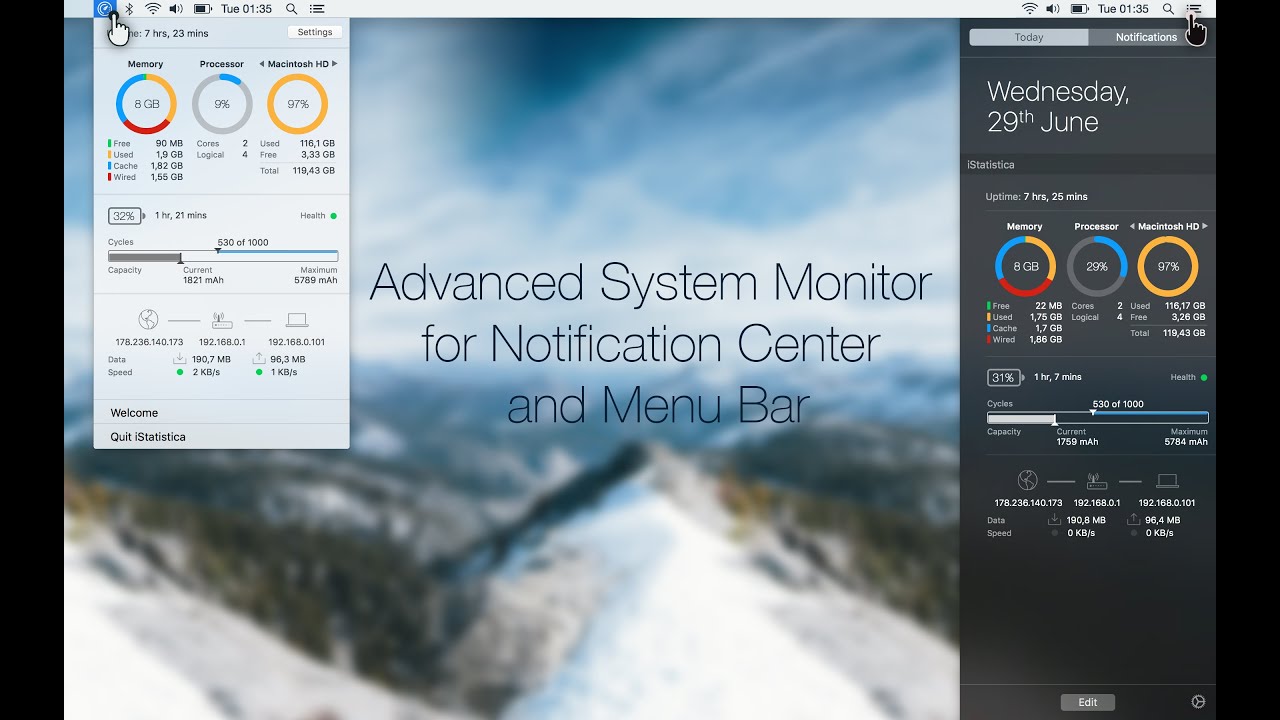
Screenshots:
Istatistica 1 2 2 – Advanced System Monitor Software
- Title: iStatistica Pro 3.0.1
- Developer: Andrey Tsarkov
- Compatibility: OS X 10.11 or later, 64-bit processor
- Language: English
- Includes: K'ed by TNT
- Size: 15.46 MB
- visit official website